G. Foletto1, F. Picciariello1, C. Agnesi1, P. Villoresi1, and G. Vallone1
Phys. Rev. A 105, 012603 (2022)
DOI:10.1103/PhysRevA.105.012603
1Department of Information Engineering, University of Padova, via Gradenigo 6/B, 35131 Padova, Italy
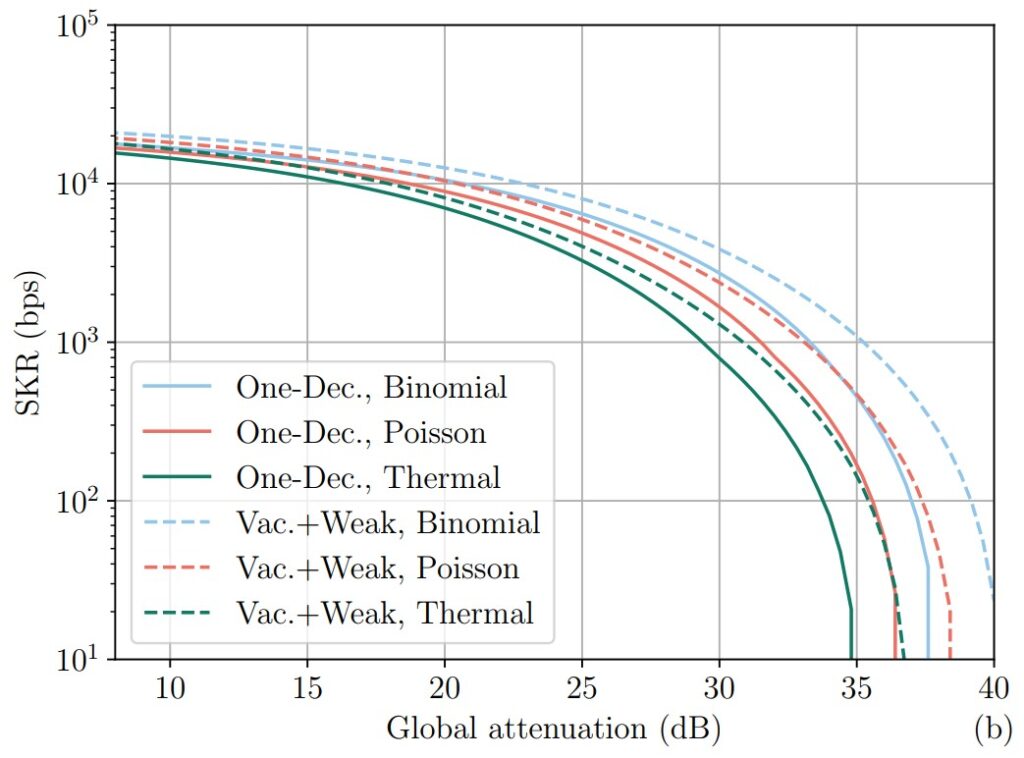
The decoy-state method is a standard enhancement to quantum key distribution (QKD) protocols that has enabled countless QKD experiments with inexpensive light sources. However, new technological advancements might require further theoretical study of this technique. In particular, the decoy-state method is typically described under the assumption of a Poisson statistical distribution for the number of photons in each QKD pulse. This is a practical choice, because prepare-and-measure QKD is often implemented with attenuated lasers, which produce exactly this distribution. However, sources that do not meet this assumption are not guaranteed to be compatible with decoy states. In this work, we provide security bounds for decoy-state QKD using a source with an arbitrary photon emission statistic. We consider both the asymptotic limit of infinite key and the finite-size scenario, and evaluate two common decoy-state schemes: the vacuum+weak and one-decoy protocols. We numerically evaluate the performance of the bounds, comparing three realistic statistical distributions (Poisson, thermal, binomial), showing that they are all viable options for QKD.
